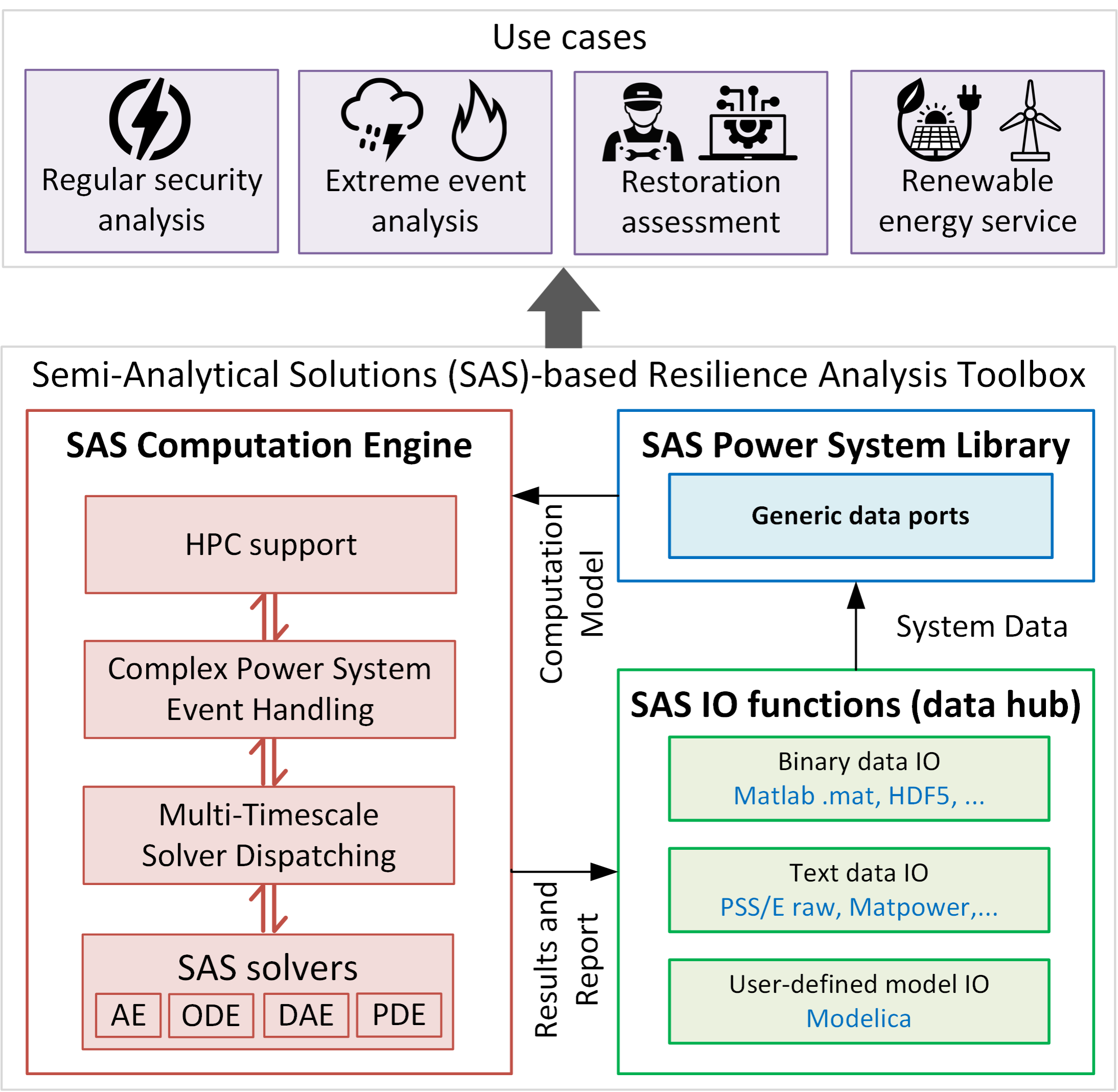
A Novel Security Analysis Toolbox for National Grid Resilience Modeling | Argonne National Laboratory
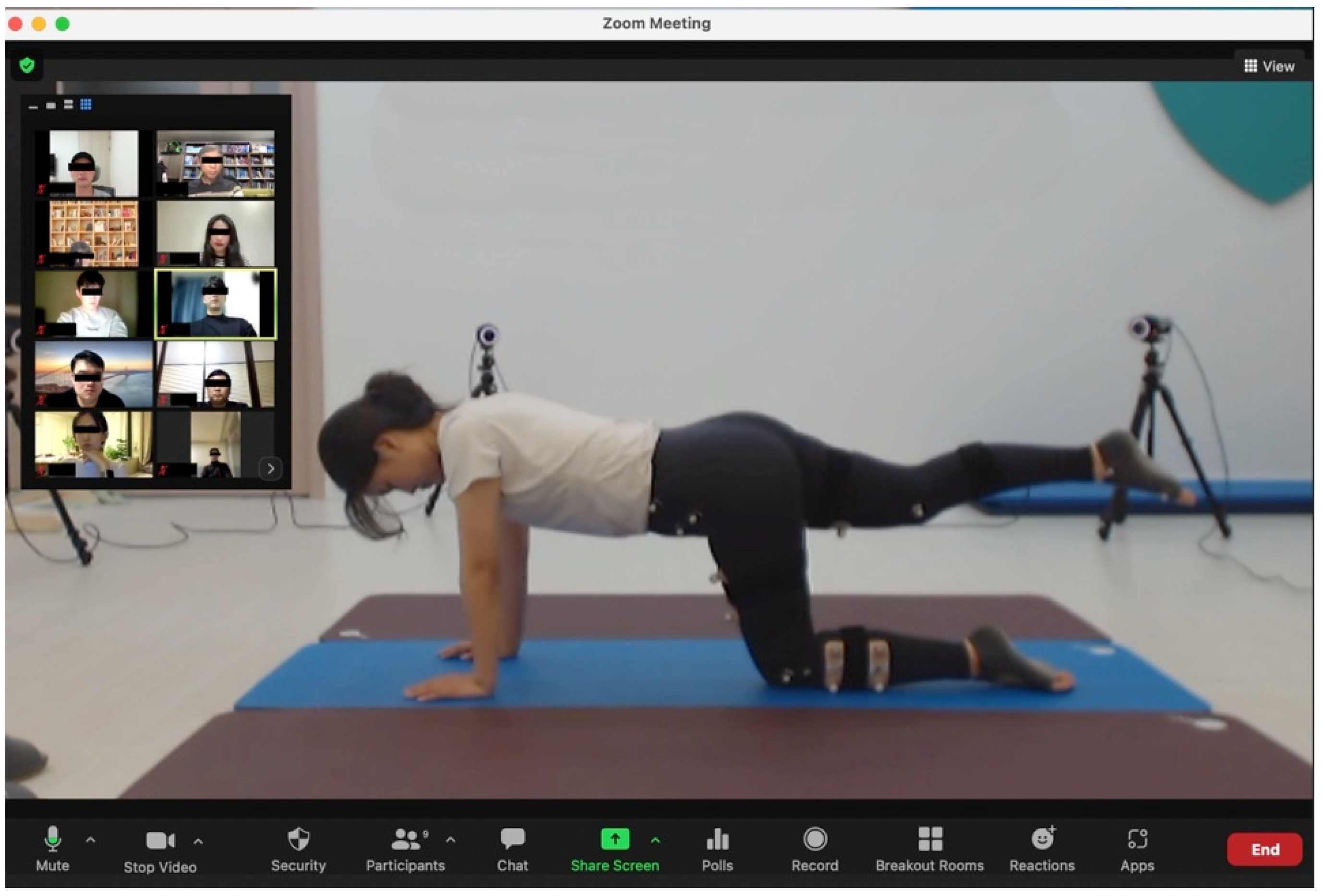
Healthcare | Free Full-Text | Agreement between 3D Motion Analysis and Tele- Assessment Using a Video Conferencing Application for Telerehabilitation

Mathematics | Free Full-Text | Cyber Security for Detecting Distributed Denial of Service Attacks in Agriculture 4.0: Deep Learning Model
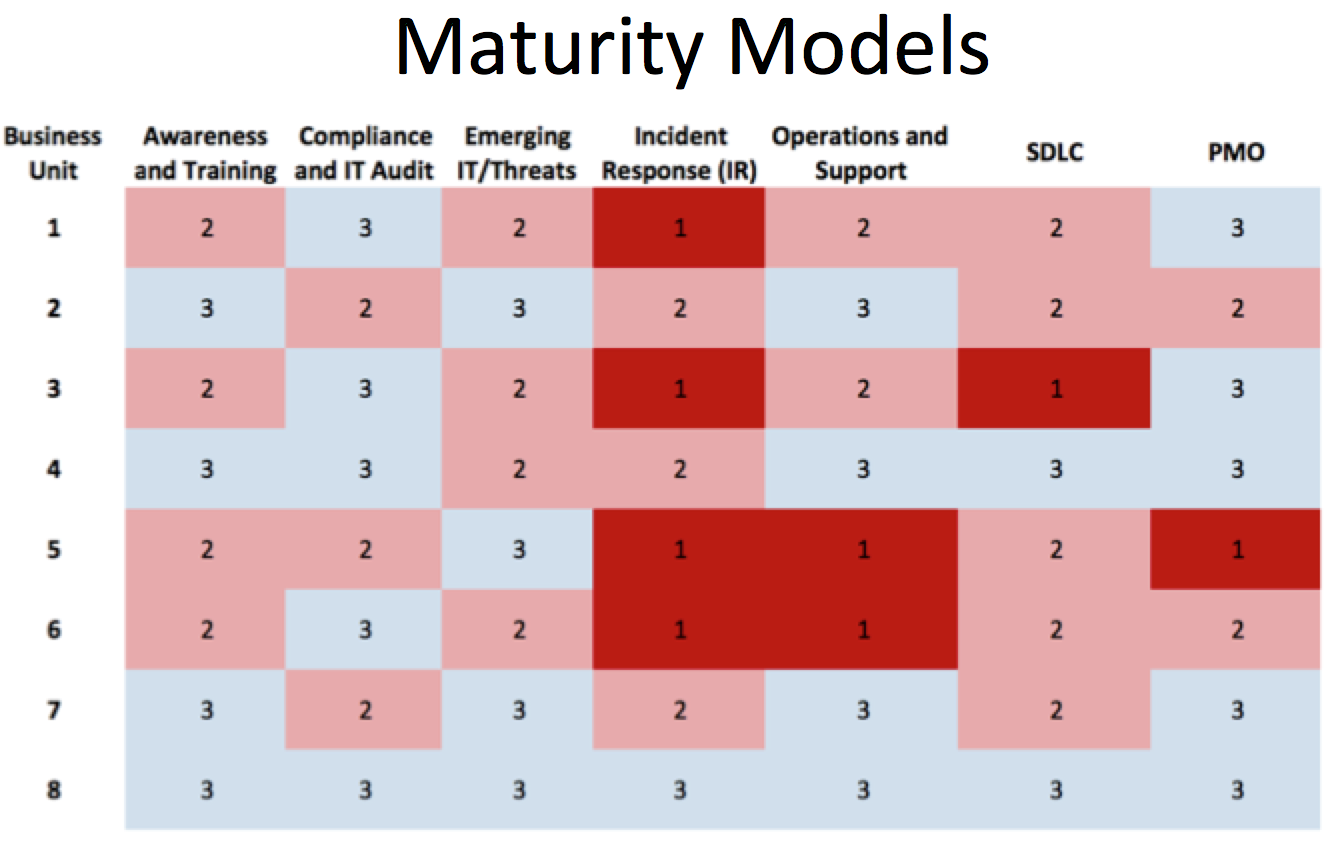
BACHELOR OF SCIENCE IN CYBER & DATA SECURITY TECHNOLOGY ANNUAL ASSESSMENT PLAN & FINDINGS 2020-2021 ACADEMIC YEAR

The general process for the definition of a cybersecurity strategy and... | Download Scientific Diagram






![Mail Security Risk Assessment & SOP Planning [VIDEO] Mail Security Risk Assessment & SOP Planning [VIDEO]](https://www.raysecur.com/wp-content/uploads/Mail-Security-Risk-Assessment-SOP-Planning-3-Policy-Documentation.jpg)





